Cybersecurity: DHS and Selected Agencies Need to Address Shortcomings in Implementation of Network Monitoring Program
Fast Facts
DHS gives agencies cybersecurity tools that identify the hardware and software on their networks and check for vulnerabilities and insecure configurations.
We reviewed how 3 agencies—the Federal Aviation Administration, Indian Health Service, and the Small Business Administration—used these tools. These agencies' hardware inventories were missing information and contained duplicates. For example, one agency's tools provided at least 2 identifiers for about 40% of the hardware on its network—leading to inventory duplicates.
Our recommendations include one for DHS to ensure that contractors configure tools to provide unique hardware identifiers.

Highlights
What GAO Found
Selected agencies—the Federal Aviation Administration, Indian Health Services, and Small Business Administration—had generally deployed tools intended to provide cybersecurity data to support the Department of Homeland Security's (DHS) Continuous Diagnostics and Mitigation (CDM) program. As depicted in the figure, the program relies on automated tools to identify hardware and software residing on agency networks. This information is aggregated and compared to expected outcomes, such as whether actual device configuration settings meet federal benchmarks. The information is then displayed on an agency dashboard and federal dashboard.
Continuous Diagnostics and Mitigation Program Data Flow from Agencies to the Federal Dashboard
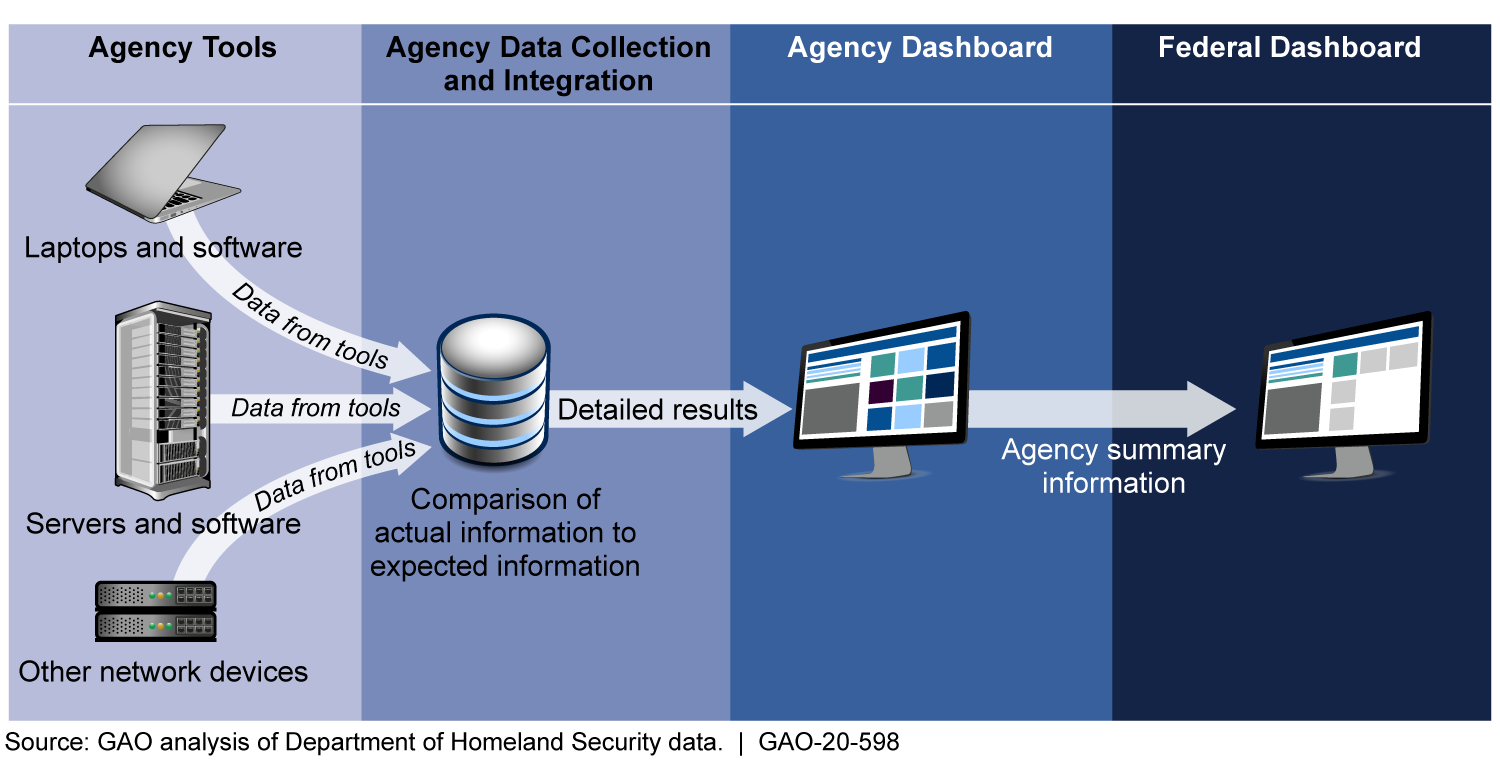
However, while agencies reported that the program improved their network awareness, none of the three agencies had effectively implemented all key CDM program requirements. For example, the three agencies had not fully implemented requirements for managing their hardware. This was due in part to contractors, who install and troubleshoot the tools, not always providing unique identifying information. Accordingly, CDM tools did not provide an accurate count of the hardware on their networks. In addition, although most agencies implemented requirements for managing software, they were not consistently comparing configuration settings on their networks to federal core benchmarks intended to maintain a standard level of security.
The agencies identified various challenges to implementing the program, including overcoming resource limitations and not being able to resolve problems directly with contractors. DHS had taken numerous steps to help manage these challenges, including tracking risks of insufficient resources, providing forums for agencies to raise concerns, and allowing agencies to provide feedback to DHS on contractor performance.
Why GAO Did This Study
In 2013, DHS established the CDM program to strengthen the cybersecurity of government networks and systems by providing tools to agencies to continuously monitor their networks. The program, with estimated costs of about $10.9 billion, intends to provide capabilities for agencies to identify, prioritize, and mitigate cybersecurity vulnerabilities.
GAO was asked to review agencies' continuous monitoring practices. This report (1) examines the extent to which selected agencies have effectively implemented key CDM program requirements and (2) describes challenges agencies identified in implementing the requirements and steps DHS has taken to address these challenges.
GAO selected three agencies based on reported acquisition of CDM tools. GAO evaluated the agencies' implementation of CDM asset management capabilities, conducted semi-structured interviews with agency officials, and examined DHS actions.
Recommendations
GAO is making six recommendations to DHS, including to ensure that contractors provide unique hardware identifiers; and nine recommendations to the three selected agencies, including to compare configurations to benchmarks. DHS and the selected agencies concurred with the recommendations.
Recommendations for Executive Action
| Agency Affected | Recommendation | Status |
|---|---|---|
| Department of Homeland Security | The Secretary of Homeland Security should ensure that integrators' solutions provide unique identifiers for hardware on selected agencies' networks. (Recommendation 1) |
We verified that DHS ensured integrators' solutions provide unique identifiers for hardware on selected agencies' networks.
|
| Department of Homeland Security | The Secretary of Homeland Security should ensure that FAA's system integrator records FISMA system information in the agency's CDM tools. (Recommendation 2) |
We verified that DHS ensured FAA's system integrator records FISMA system information in the agency's CDM tools.
|
| Department of Homeland Security | The Secretary of Homeland Security should ensure that IHS's system integrator records FISMA system information in the agency's CDM tools. (Recommendation 3) |
We verified that DHS ensured that IHS's system integrator records FISMA system information in the agency's CDM tools.
|
| Department of Homeland Security | The Secretary of Homeland Security should ensure that FAA's system integrator establishes a process to integrate all vulnerability information in the agency's CDM tools, including the time a vulnerability was remediated. (Recommendation 4) |
We verified that DHS ensured that FAA's system integrator established a process to integrate all vulnerability information in the agency's CDM tools, including the time a vulnerability was remediated.
|
| Department of Homeland Security | The Secretary of Homeland Security should ensure that IHS's system integrator establishes a process to integrate all vulnerability information in the agency's CDM tools, including the time a vulnerability was remediated. (Recommendation 5) |
We verified that DHS ensured that IHS's system integrator established a process to integrate all vulnerability information in the agency's CDM tools, including the time a vulnerability was remediated.
|
| Department of Homeland Security | The Secretary of Homeland Security should ensure that SBA's system integrator establishes a process to integrate all vulnerability information in the agency's CDM tools, including the time a vulnerability was remediated. (Recommendation 6) |
We verified that DHS ensured SBA's system integrator updated the agency's CDM tools to capture vulnerability information, including the time a vulnerability was remediated.
|
| Federal Aviation Administration | The FAA Administrator should commit to a time frame to complete the agency's effort to associate hardware with its FISMA systems. (Recommendation 7) |
We verified that FAA established a time frame to complete the agency's effort to associate hardware with its FISMA systems.
|
| Federal Aviation Administration | The FAA Administrator should document agency-specific variations from federal core configuration benchmarks for each operating system on its network. (Recommendation 8) |
We verified that FAA documented agency-specific variations from federal core configuration benchmarks for each operating system on its network.
|
| Federal Aviation Administration | The FAA Administrator should configure its CDM tools to compare configuration settings against federal core benchmarks and agency-specific variations applicable to its environment. (Recommendation 9) |
We verified that FAA configured its CDM tools to compare configuration settings against federal core benchmarks and agency-specific variations applicable to its environment.
|
| Indian Health Service | The Director of IHS should document approved hardware inventory information by associating FISMA systems with the hardware on its network in a format that can be readily integrated into its CDM tools. (Recommendation 10) |
As of August 2024, the Indian Health Service has not provided sufficient evidence to close this recommendation. When we confirm what actions IHS has taken we will provide updated information.
|
| Indian Health Service | The Director of IHS should document agency-specific variations from federal core configuration benchmarks for each operating system on its network. (Recommendation 11) |
We verified that IHS documented agency-specific variations from federal core configuration benchmarks for each operating system on its network.
|
| Indian Health Service | The Director of IHS should configure its CDM tools to compare configuration settings against federal core benchmarks applicable to its environment. (Recommendation 12) |
As of August 2024, the Indian Health Service has not provided sufficient evidence to close this recommendation. When we confirm what actions IHS has taken we will provide updated information.
|
| Small Business Administration | The SBA Administrator should commit to a time frame to complete the agency's effort to associate hardware with its FISMA systems. (Recommendation 13) |
We verified that SBA completed efforts to associate hardware with its FISMA systems.
|
| Small Business Administration | The SBA Administrator should document agency-specific variations from federal core configuration benchmarks for each operating system on its network. (Recommendation 14) |
We verified that SBA documented agency-specific variations from federal core configuration benchmarks for each operating system on its network.
|
| Small Business Administration | The SBA Administrator should configure its CDM tools to compare configuration settings against agency-specific benchmarks applicable to its environment. (Recommendation 15) |
We verified that SBA configured its CDM tools to compare configuration settings against agency-specific benchmarks applicable to its environment.
|